Security measures¶
Data encryption¶
Data stored on Fudo PAM is encrypted with AES-XTS algorithm using 256 bit encryption keys. AES-XTS algorithm is most effective hard drive encryption solution.
Appliance
Encryption keys are stored on two USB flash drives. Flash drives delivered with Fudo PAM are uninitialized. Keys initialization takes place during initial system boot-up, during which both flash drives have to be connected (initiation procedure is described in chapter System initiation).
After encryption keys have been initiated and Fudo PAM has booted up, both USB flash drives can be removed and placed somewhere safe. During daily operation, encryption key is required only for system boot up. If safety procedures allow, one USB flash drive can stay connected to Fudo PAM, which will allow Fudo PAM to boot up automatically in case of a power outage or system reboot after software update.
Virtual machine distribution
Fudo PAM’s file system, running in virtual environment is encrypted using an encryption phrase, which is set up during system initiation and has to be entered each time the system boots up.
Permissions¶
Each data model entity, has a list of users defined, who are allowed to manage given object, according to assigned user role.
For more information on user roles refer to Roles topic.
Sandboxing¶
Fudo PAM takes advantage of CAPSICUM sandboxing mechanism, which separates each connection on Fudo PAM operating system level. Precise control over assigned system resources and limiting access to information on the operating system itself, increase security and greatly influence system’s stability and availability.
Reliability¶
System hardware configuration is optimized to deliver high performance and high availability.
Cluster configuration¶
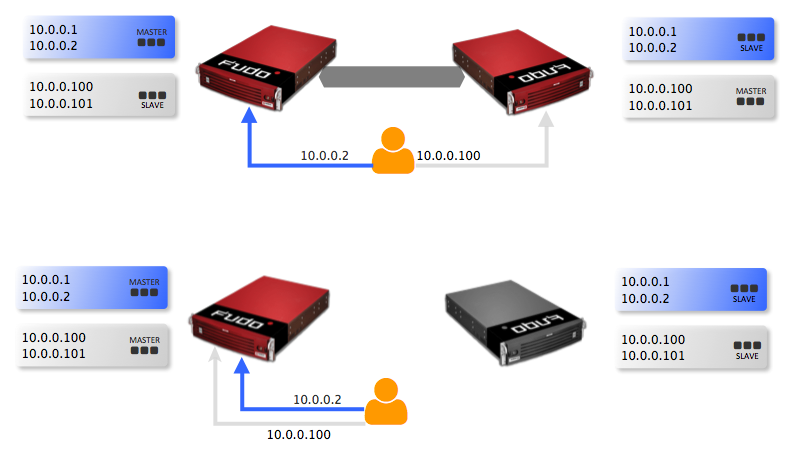
Fudo PAM supports cluster configuration in multimaster mode where system configuration (connections, servers, sessions, etc.) is synchronized on each cluster node and in case a given node crashes, remaining nodes will immediately take over user connection requests ensuring service continuity.
Warning
Cluster configuration does not facilitate data backup. If session data is deleted on one of the cluster nodes, it is also deleted from other nodes.
Virtual IP addresses are aggregated in redundancy groups which enable facilitating static load balancing while preserving cluster’s high availability nature.
Related topics: