Data model migration from Wheel Fudo PAM version 2.2 to 3.0¶
This topic describes data model migration mechanisms that are applied when performing upgrade from Wheel Fudo PAM version 2.2 to 3.0.
Note
In case of unsuccessful upgrade to version 3.0 data model issues which caused upgrade procedure to fail can be found in the system evetns log.
Server¶
Servers, which have the same IP address and port number assigned are replaced with a single object. Name of the resulting object is a concatenation of the servers’ names in ascending order, separated by comma.
Warning
If there are two servers with the same IP address and port number assigned but with different protocol, description, external password repositorie, RDP security level, HTTP settings, TLS settings, certificates or public keys, upgrade will fail.
Safe (previously connection)¶
- Anonymous connection becomes a safe object, which can be deleted.
- For each bastion object (a group of servers operating in bastion mode, assigned to the same bastion) and associated connection, there is a safe object created using the following naming convention:
<connection name> > <bastion name>. - For each server operating in gateway, proxy or transparent mode, migration procedure creates a safe object named
<connection name> > <server name. - Automatically created safe object inherits connection’s access rights, granted privileges, protocols settings, notifications settings and LDAP mapping.
- OCR settings, sessions recording and session data retention parameters are moved to corresponding account objects.
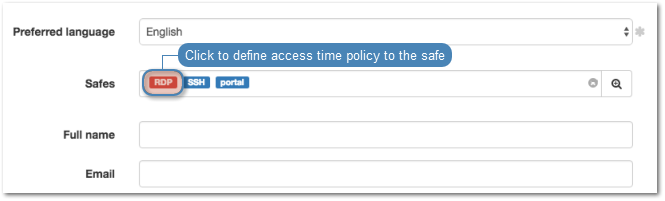
- Time policies are replicated as user specific regulations applicable to each safe.
Note
Click selected safe on user’s configuration form to display time access settings.
- After migration, login credentials policies are reflected within the safe.
Account (previously login credentials)¶
For each login credentials sections in every connection, migration mechanism creates a separate account object.
- If login credentials contain the user login string the resulting account is of the regular type and its name is a combination of the login and server’s name -
<login> @ <final server name>. - If login credentials do not contain the user login string and concern credentials forwarding connection, the resulting account object is of the forward type and it is named
forward for <final server name>. - If login credentials do not contain the user login and are used for anonymous connections, the resulting account object is of the anonymous type and it is named
anonymous for <final server name>. - Duplicated loign credentials are replaced by a single account object. Object’s management rights, OCR settings, sessions recording settings, session data retention settings are inherited from the connection object that the account object derives from.
Warning
If login credentials contain the login string but do not contain the secret (if the login is substituted but the secret field remains empty) the data migration process will fail.
Listener (previously bastion or part of a server)¶
- For each server operating in proxy, transparent or gateway mode, there is a listener object created with the same connection mode.
- Newly created object inherits server’s access rights, TLS settings and RDP security level parameter.
- Server announcement setting is also passed on to the listener object.
- Listener is assigned to all safes that have been created based on connections which were associated with the server that the listener derived from.
- Bastion becomes a listener operating in the bastion mode. Access rights and bastion settings are transferred to the listener. The listener is assigned to all safes that have been created based on connections associated with at least one server from the bastion that the listener derived from.
Sessions¶
- Each session has its safe, server and account identifiers updated accordingly. If a session concerned a server, which was not operating in bastion mode, it also has the listener identifier set.