Users¶
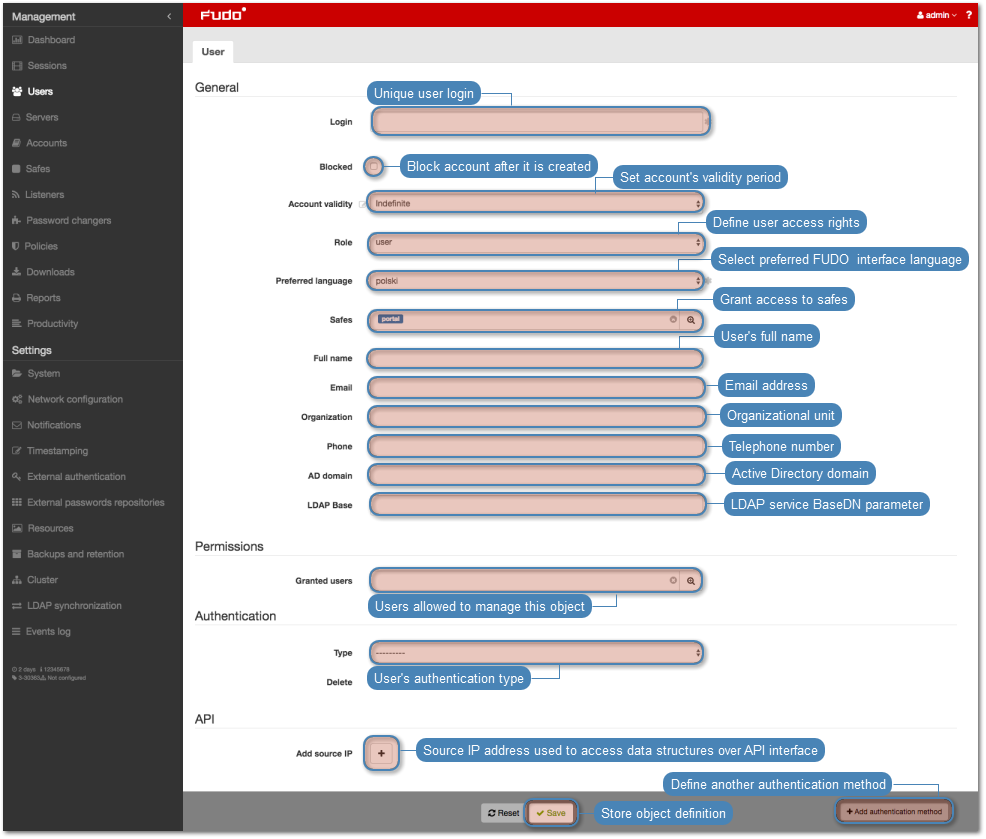
User defines a subject entitled to connect to servers within monitored IT infrastructure. Detailed object definition (i.e. unique login, full name, email address etc.) enables precise accountability of user actions when login and password are substituted with a shared account login credentials.
Note
Wheel Fudo PAM allows importing users definitions from directory services such as Active Directory or LDAP. For more information on users synchronization service, refer to the Users synchronization topic.
Adding a user¶
Warning
Data model objects: safes, users, servers, accounts and listeners are replicated within the cluster and object instances must not be added on each node. In case the replication mechanism fails to copy objects to other nodes, contact technical support department.
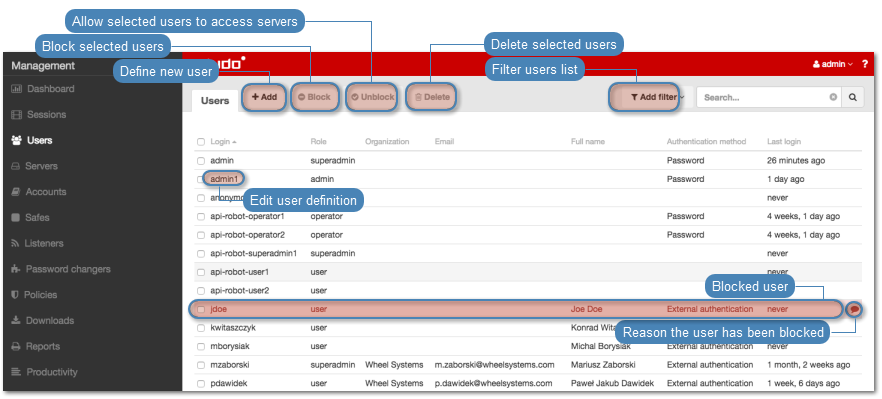
- Select > .
- Click .
Note
Wheel Fudo PAM enables creating users based on the existing definitions. Click desired user to access its configuration parameters and click to create a new object based on the selected definition.
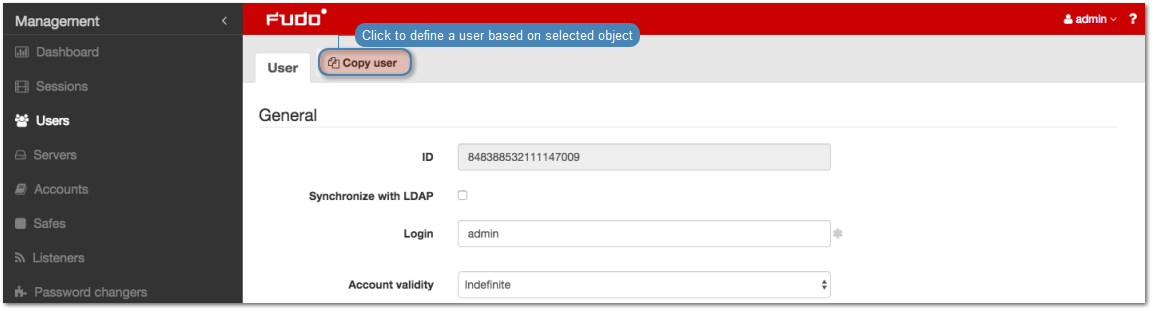
- Enter user unique login.
Note
The Login field is not case sensitive.
- Select the Blocked option to disable user account after it is created.
- Define account’s validity period.
- Select user’s role, which will determine the access rights.
Note
Access rights restrictions also apply to API interface access.
| Role | Access rights |
|---|---|
| user | Connecting to servers as defined in connections, to which the user has been assigned. |
| operator |
|
| admin |
|
| superadmin |
|
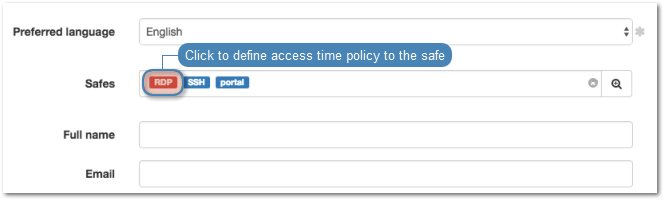
- Select user’s preferred language in Wheel Fudo PAM administration panel.
- Grant access to safes.
- Define time access policy.
- Click desired safe object.
- Select Enable time policy option.
- Click the weekly calendar to define time interval.
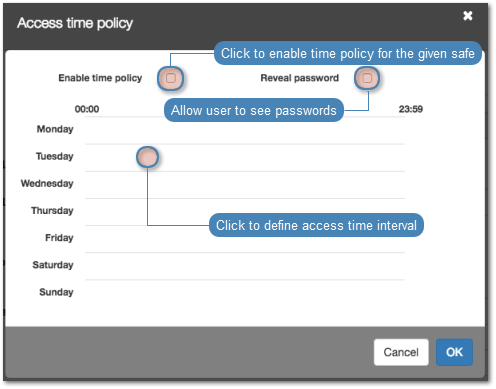
- Click .
- Enter user’s full name.
- Enter user’s email address.
- Enter user’s organizational unit.
- Enter user’s phone number.
- Provide user’s Active Directory domain.
- Enter LDAP service BaseDN parameter.
- In the Permissions section, select users allowed to manage this user object.
- In the Authentication section, select authentication type.
External authentication
- Select
External authenticaitonfrom the Type drop-down list. - Select external authentication source from the External authentication source drop-down list.
Note
Refer to External authentication topic for more information on external authentication sources.
Password
- Select
Passwordfrom the Type drop-down list. - Type password in the Password field.
- Repeat password in the Repeat password field.
SSH key
- Select
SSH keyfrom the Type drop-down list.
- Click i icon and browse the file system to find the public SSH key used for verifying user’s identity.
One-time password
Warning
One-time passwords are used for implementing AAPM use case scenarios.
- Select
One-time passwordfrom the Type drop-down list.
- Click to define more authentication methods.
- Click .
Editing a user¶
- Select > .
- Find desired user definition.
- Click user’s login to access its configuration parameters.
- Modify configuration parameters as desired.
Note
Unsaved changes are marked with an icon.
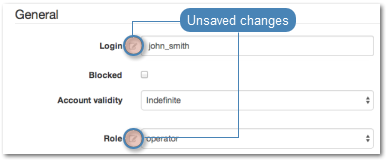
- Click .
Blocking and unblocking a user
Warning
Blocking a user will terminate its current connections.
- Select > .
- Find and select the desired user definition.
- Click to disallow the user to connect to servers or to allow user to connect to servers.
- Provide a descriptive reason for blocking the given user and click .
Deleting a user¶
Warning
Deleting a user definition will terminate its current connections.
- Select > .
- Find and select the desired user definition.
- Click .
- Confirm resource deletion.
Roles¶
| Role | Access rights |
|---|---|
| user | Connecting to servers as defined in connections, to which the user has been assigned. |
| operator |
|
| admin |
|
| superadmin |
|
Related topics: